Zero views on a fresh TikTok account? Facebook Ad accounts wiped out overnight? Hit with a sudden Amazon “linked account” suspension?
Most beginners panic and assume they accidentally broke a platform rule. But the truth is, if your operations are clean, the underlying issue is usually your network environment. If your digital footprint is compromised, no amount of careful account warm-up will save you.
To bypass these strict risk-control systems, you need a proxy IP. This article will break down what a proxy IP is, how it works, its core classifications, and how to choose the right one for your exact needs.
What is a Proxy IP?
To truly understand this, we first need to clear up the confusion between two closely related terms: the “Proxy Server” and the “Proxy IP.”
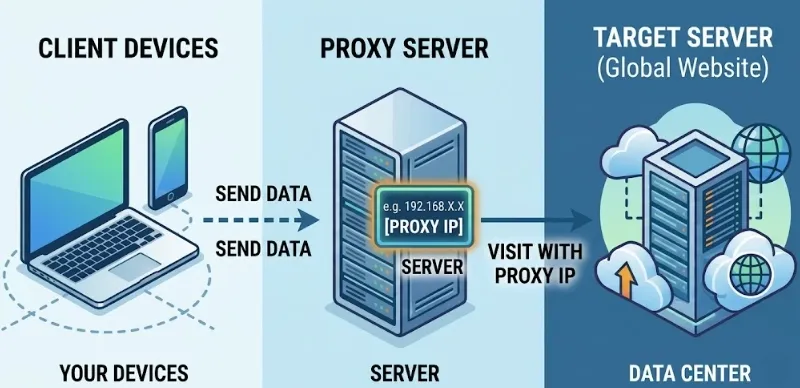
In a standard network setup, a proxy server acts as a middleman. It sits directly between your device and the target website you are trying to reach. The proxy IP is simply the unique internet address assigned to that middleman server.
The phrase ‘buying proxy IPs’, which we often talk about in the cross-border industry, essentially means renting the rights to use a specific proxy server, allowing our network data to pass through it.
How Does a Proxy IP Work?
We can break down its complete workflow into the following five steps:
1. Sending a request: When you operate on your computer or mobile phone (such as opening TikTok or Amazon), your device first sends a network access request.
2. Receiving by the proxy server: This request is not sent directly to the target website but is first transmitted to the proxy server you have configured in advance.
3. Replacing the real IP: After receiving the request, the proxy server strips the real network information (your local IP address) and replaces it in the request with its own “proxy IP”.
4. Accessing the target website: Then, the proxy server, with this new network identity, requests data from the target website on behalf of your device.
5. Returning the data: The target website packages the web page content and sends it to the proxy server. Finally, the proxy relays that information right back to your device.
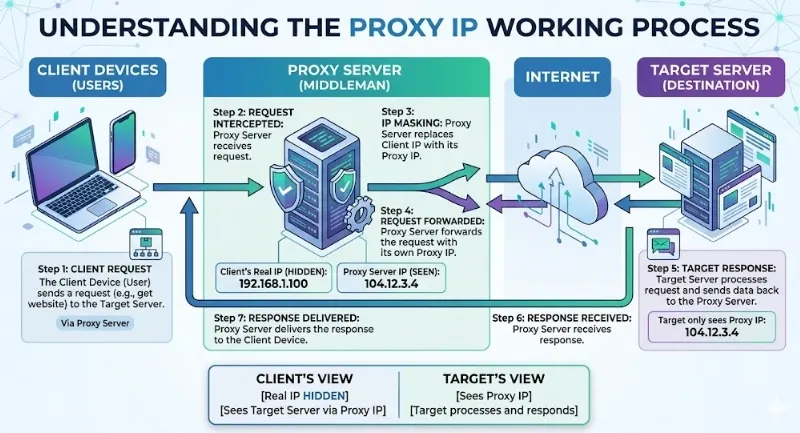
Through this seamless back-and-forth process, the proxy acts as a shield—completely hiding your real identity and keeping your digital footprint secure.
Proxy IP vs. VPN: What is the Difference?
Beginners often confuse proxy IPs with VPNs, but they serve different core purposes. A VPN encrypts your entire device’s network traffic at the operating system level. A proxy IP, on the other hand, operates at the application level.
To make the distinction clearer, here is a quick breakdown:
| Core Feature | Proxy IP | VPN (Virtual Private Network) |
|---|---|---|
| Operating Level | Application Level (targets specific browsers, anti-detect profiles, or scripts). | OS Level (forces all device traffic through a single tunnel). |
| Primary Focus | Massive scalability, precise geo-targeting, and rapid IP rotation. | Personal privacy and heavy data encryption. |
| IP Rotation | Highly flexible. Can rotate automatically per request or stay static. | Rigid. Usually locks you to a single server until you manually disconnect. |
| Resource Drain | Lightweight and fast, perfect for high-concurrency tasks. | Heavy encryption protocols can noticeably slow down network speeds. |
| Ideal Scenarios | Multi-store management, bulk SEO scraping, local ad verification. | Securing public Wi-Fi connections, bypassing basic streaming geo-blocks. |
Types of Proxy IPs
Proxy IPs come in many forms. Below, we break them down by four key factors.
1.By IP Source
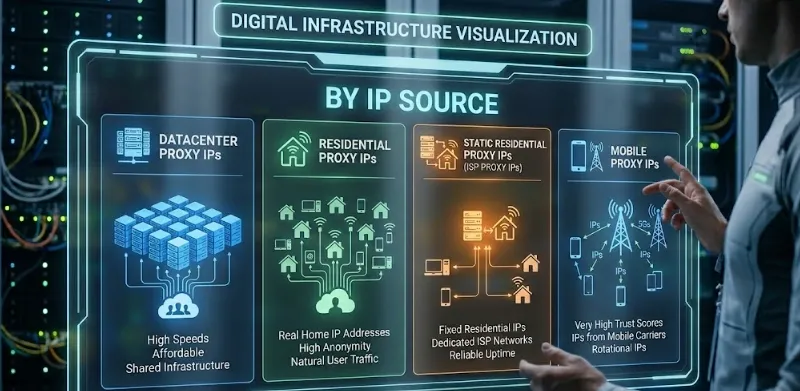
Datacenter Proxy IPs
Key Features: These IPs are generated in bulk by large cloud service providers and data centers (like AWS, Google Cloud, or Azure).
Pros: Fast speeds and rock-solid stability, thanks to commercial fiber-optic networks. Because they are mass-produced on servers, they are the cheapest option on the market.
Cons: Their ASN belongs to a hosting company, not a standard residential ISP. Strict platforms like Amazon or Facebook can instantly flag them as server traffic. This leads to a massive risk of CAPTCHAs and immediate account bans.
Best for: Basic tasks that don’t require high IP purity, such as scraping public data at scale or initial market research. Never use them for logging into or warming up high-value accounts.
Residential Proxy IPs
Key Features: These nodes come straight from real home Wi-Fi networks. They are IP addresses assigned to everyday homeowners by local Internet Service Providers (like Comcast or AT&T).
Pros: Maximum authenticity. Target websites see these requests as coming from a regular person sitting in their living room.
Cons: Speeds and connection stability are lower than datacenter proxies, and they are more expensive.
Best for: Managing multi-store e-commerce setups, daily social media posting, copping limited-edition goods, and stealthy competitor price monitoring.
Static Residential Proxy IPs (ISP Proxy IPs)
Key Features: A hybrid proxy that combines the best of both worlds. The IP is officially assigned by a consumer ISP (giving it human trust), but the server itself is hosted in a commercial data center.
Pros: Offers the “high trust score” of a residential IP coupled with the “extreme speed and uptime” of a datacenter proxy.
Cons: The premium architecture means these plans come at a high cost.
Best for: E-commerce multi-account management and nurturing core social media accounts.
Mobile Proxy IPs
Key Features: Sourced directly from mobile network operators (like T-Mobile or Verizon), using real 4G/5G cell tower IPs.
Pros: The absolute highest trust score on the internet. Platforms rarely ban mobile IPs because doing so would accidentally block massive amounts of legitimate users.
Cons: The most expensive type of proxy to source. Speeds can be highly volatile since they depend entirely on local cellular signal strength.
Best for: Registering and warming up accounts on platforms with the strictest risk-control systems (like Facebook, X, Instagram, and TikTok).
2.By Anonymity Level
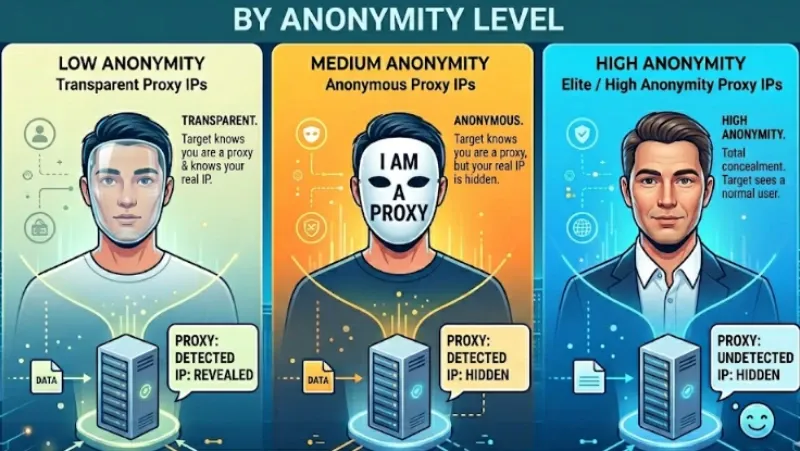
Transparent Proxy IPs
Key Features: The target website knows you are using a proxy and can directly read your real IP address in the underlying network request (like wearing a clear mask—everyone sees right through it).
Pros: Almost zero extra resource drain
Cons: Cannot hide your identity, offering zero privacy protection
Best for: Usually used by schools or corporate intranets to bypass local access restrictions or monitor web behavior
Anonymous Proxy IPs
Key Features: The target website knows you are hiding your location using a proxy, but it cannot see your real IP (like wearing a mask labeled “I am a proxy”).
Pros: Hide your real location.
Cons: Easily triggers extra security challenges on strict websites due to proxy tags.
Best for: Basic privacy protection and bypassing geo-restrictions on public webpages.
Elite / High Anonymity Proxy IPs
Key Features: The target website has no idea you are using a proxy and cannot see your real IP; it assumes the proxy IP is your actual IP address (the perfect disguise).
Pros: Offers the highest level of privacy protection and the lowest block rates.
Cons: Requires higher technical capabilities from the provider compared to transparent proxies.
Best for: Almost all commercial use cases (e.g., SEO matrices, bulk social media account management, secure isolation for e-commerce stores, and overseas market research).
3.By Network Protocol
HTTP Proxy IPs
Key Features: Designed specifically for web browser traffic.
Pros: Versatile, fast parsing speeds.
Cons: Single-purpose; only handles HTTP traffic.
Best for: Standard web scraping and browsing.
HTTPS Proxy IPs
Key Features: Adds an encryption layer over HTTP, supporting secure transmission.
Pros: Encrypts all data transfers to prevent man-in-the-middle attacks.
Cons: Encryption causes a negligible performance dip.
Best for: Accessing secure sites, financial transactions, and transmitting sensitive data.
SOCKS5 Proxy IPs
Key Features: A lower-level protocol that supports web traffic, as well as TCP and UDP streams.
Pros: Fast and works with almost any application type.
Cons: Does not rewrite HTTP headers (meaning less optimization for specific web content).
Best for: Gaming acceleration, client software routing, complex automation scripts, and P2P/BitTorrent downloads.
4.By Lifespan and Allocation Method
Static / Dedicated Proxy IPs
Key Features: The proxy IP address remains fixed and is exclusively yours for the duration of the lease.
Pros: Extremely stable for building long-term “environment trust.”
Cons: If the single IP gets banned, your associated business operation is disrupted.
Best for: Operations requiring a consistently stable environment, like e-commerce stores and social media account nurturing.
Dynamic / Rotating Proxy IPs
Key Features: The proxy server provides an entry point, but your outbound IP constantly changes (rotating with every request or every few minutes).
Pros: Easily bypasses rate limits targeted at single IPs, making detection incredibly difficult.
Cons: Cannot maintain long-term persistent login sessions.
Best for: Large-scale web scraping, data harvesting, high-frequency price comparison systems, and bulk account registration.
Applications of Proxy IPs
1.Cross-Border E-commerce Multi-Store Management
The Pain Point: E-commerce platforms (Amazon, Shopee, etc.) strictly monitor for “linked accounts.” If you log into multiple store dashboards from the same broadband connection, the platform can determine that these stores are operated by the same person based on the detected identical IP addresses. If one store violates a rule and gets banned, the others will be banned as well.
The Solution: Assign a dedicated static residential proxy IP to each store (usually paired with an anti-detect browser). This completely isolates the network environments during data exchange.
2. Social Media Matrices and Ad Marketing
The Pain Point: For instance, on platforms like TikTok and Facebook, if you use the same network to register dozens of accounts in bulk, or perform actions such as liking and posting simultaneously, this will immediately trigger the platform’s high-risk interception system. This could result in newly created TikTok accounts having zero views right away, or Facebook’s advertising matrix accounts suffering consecutive failures.
The Solution: Take a phased approach. For initial registration, use mobile proxy IPs or dynamic residential proxy IPs to constantly rotate IP nodes. Once the accounts enter their long-term operational phase, bind core accounts to static residential proxy IPs to maintain a consistent geo-location and steadily build trust.
3. Competitor Data Scraping and Price Monitoring
The Pain Point: Automated scripts pulling competitor pricing move much faster than a human. The target server quickly detects the abnormal traffic and blocks the IP.
The Solution: Integrate dynamic rotating proxies. Configure your scraping tool to rotate to a fresh IP with every request, distributing massive scrape requests across thousands of distinct network nodes.
4. Overseas Market Research and Local Ad Verification
The Pain Point: Many platforms show localized product pages, regional pricing, or targeted ads only to local networks. Connecting directly from your home country often results in blocked access or generic international content.
The Solution: Connect to elite proxy IPs located in your target country or city. The target website reads the expected local network data and serves the correct commercial content.
How to Choose the Right Proxy IP?
The mainstream global proxy market essentially blends the core “IP Source” and “Lifespan” to create four main products.
| Proxy Type | Best Parameter Combo | Ideal Business Scenario | Key Metrics | Avoid!!! |
|---|---|---|---|---|
| Static Residential Proxy IPs | Elite + SOCKS5 / HTTPS | 1. Store isolation: Amazon, Shopee. 2. Core asset nurturing: VIP social accounts, main ad accounts. 3. Localization: Viewing stable overseas pages. |
Exclusivity & Lifespan: Must guarantee 100% solo use during the lease and support long-term renewals to maintain network authority. | Beware of “Broadcast IPs” (cheap datacenter IPs disguised as residential). If the underlying datacenter is detected, core stores will be banned immediately. |
| Dynamic Residential Proxy IPs | Elite + SOCKS5 / HTTP | 1. Cross-border interactions: Sneaker botting, Web3 bulk actions. 2. Social media bulk actions: Matrix messaging, liking. 3. Price monitoring: Evading anti-bot systems. |
Precision & Success Rate: Must be able to target specific overseas cities. Test connection success rates during IP rotation. | High IP reuse rates. If the same IP was recently used by someone else for similar interactions, the system will flag it as bulk fraud. |
| Mobile Proxy IPs | Elite + SOCKS5 | 1. High-risk account creation: FB, TK. 2. Bypassing security reviews: Solving “zero views” or instant bans. |
Real Cell Tower Traits: Verify if it’s a genuine local carrier network. | Never touch anonymous or transparent proxies. If the underlying tag leaks, the high trust score of mobile proxies vanishes instantly. |
| Datacenter Proxy IPs | Elite + HTTP / HTTPS | 1. Mass data scraping: Python scripts on unprotected sites. 2. Basic network testing: Tasks with very low IP requirements. |
Concurrency Limits & Billing: Check for multi-threading limits. For massive scraping, paying per GB is usually cheaper. | Do not use these to nurture high-value accounts. Datacenter IPs are easily flagged; never use them to log into e-commerce dashboards. |
No matter which type you choose, if your business involves anti-linking, always choose “elite anonymity” to ensure no proxy traces leak. Also, it is advisable to prioritize SOCKS5 or HTTPS protocols for superior security.
RoxyIP: Global Proxy IPs, Zero Guesswork
The buyer’s guide above will help you dodge 90% of parameter traps. However, when you actually buy, you might still face this reality:
You pay top dollar for a premium static residential proxy IP, but the moment you bind it to your Amazon store or post a TikTok, you trigger a ban. When you ask customer service for help, they brush you off with “IPs are non-refundable once extracted.” This happens because they are middle-men resellers who don’t control the underlying resources. To stop wasting money, you must buy directly from the source.
RoxyIP owns first-hand, self-operated nodes and offers free proxy IP replacements for clients.
Our every single residential node is 100% ethically sourced with explicit user consent, keeping you fully compliant with global data privacy laws.
Strict platforms don’t just check your IP anymore. They actively hunt for WebRTC leaks, DNS mismatches, and bad ASN reputations. We don’t just promise our nodes pass these extreme checks—we prove it.
To verify their purity, we ran our nodes through the industry’s four major risk detection platforms (tested under strict variable controls without extra fingerprint interference). Here is how RoxyIP actually performs:
| Testing Platform | Core Detection Metric | Our Test Results |
|---|---|---|
| ping0.cc | Fraud Risk & Proxy Detection | Extremely Low Risk: Not flagged as a proxy/VPN; zero blacklist history. |
| ipinfo.io | IP Type & ISP | Native Residential ISP: Accurately identified as home broadband; not a hosting IP. |
| ipdata.co | Threat Intelligence & Malicious Tags | Zero Risk: Threat database shows zero tags; no malicious or crawler history. |
| scamalytics.com | E-commerce/Financial Fraud Score | All Green (Passed): Fraud score falls in the lowest bracket, passing strict security thresholds. |
RoxyIP perfectly passed every underlying security engine screening. Beyond that, RoxyIP excels in practical operations across four key areas:
Massive Scale (Industry Top-Tier): Sitting on over 90 million genuine, self-operated native nodes across 200+ countries and regions, our IP pool is the largest in the industry. Whether you need pure static dedicated IPs in the US/EU or dynamic rotating IPs in Southeast Asia, we guarantee precise geolocation targeting.
Blazing Fast (Dedicated Lines): Designed for high-frequency social media engagement and e-commerce backend management, we use dedicated high-speed underlays supporting custom 100Mbps bandwidth. Perfectly optimized for Facebook, TikTok, Reddit, and YouTube—say goodbye to infinite loading screens and sluggish video uploads.
Rock Solid Reliability: All nodes pass rigorous historical purity screenings. With a 98% business success rate and a strict “no success, no charge” policy, we provide the ultimate anti-linking barrier.
Unbeatable Cost-Efficiency: Offering the best prices in the industry. We dramatically lower the marginal costs of large-scale store deployments and matrix nurturing while guaranteeing a 100% pure network experience.
Summary & Practical Pitfalls to Avoid
1.Never fall for “Lifetime Free IPs”: There is no free lunch; free proxy IPs are the most expensive. These IPs have usually been abused by black-hat operations, are blacklisted, and will trigger instant bans.
2.One Account, One IP: We strongly recommend binding one browser environment (for one critical account) strictly to one proxy IP. Never log in with a US IP today and a UK IP tomorrow.
3.Test Connectivity Before Bulk Purchasing: Buy the lowest-tier package to test connectivity and speeds before committing to massive bulk orders.
4.Choosing the Right Type: Static ISP proxies are best for accounts requiring long-term, stable logins; Dynamic residential proxies are ideal for mass registration, scraping, or data harvesting.
5.Optimize Your Billing Model: Match your billing to your exact use case. For SEO scraping (frequent rotation, low data consumption), paying per GB is usually best. But for TikTok matrices or idling e-commerce dashboards, buying by IP count or time duration is much safer and cheaper.
Final Note: Relying solely on a premium proxy IP won’t completely solve ban problems. A proxy only masks your “network environment,” but platforms also check your “device environment.” The ultimate solution to eradicate account linking and bans is combining a pure proxy IP with an anti-detect browser.
FAQs
1.What is the proxy IP?
A proxy IP acts as an intermediary server between your device and the internet. It receives your web requests, forwards them to the target website, and returns the data to you, keeping your real identity hidden.
2.How do I find my proxy IP?
The easiest way is to visit an IP-checking website like whatismyip.com or ipinfo.io while connected. You can also find it in your operating system’s network settings or your anti-detect browser’s profile configuration.
3.Is proxy legal or illegal?
Using a proxy is completely legal in most countries. However, using a proxy to commit illegal acts (such as fraud, cyberattacks, or copyright infringement) is illegal.
4.What is a proxy IP address?
It is the unique numerical identifier (IPv4 or IPv6) assigned to the proxy server. Think of it as a public PO Box that masks your real “home address” (your local IP) from the websites you visit.
5.How to use proxy IP?
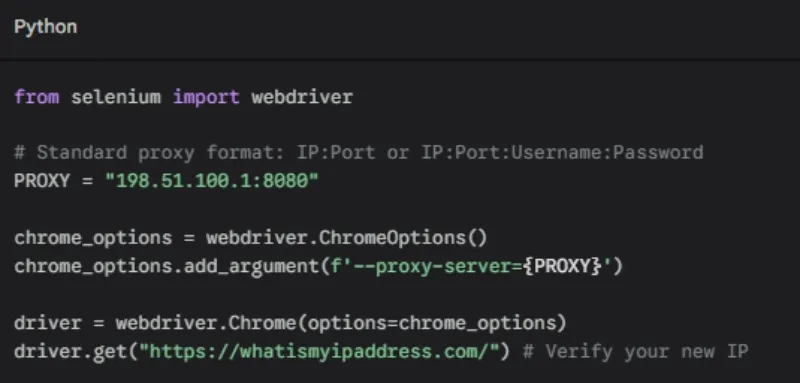
You can configure a proxy in several ways:
Enter the IP and port in your operating system’s network settings.
Use a browser extension (like SwitchyOmega) for quick toggling.
Input the proxy credentials into an anti-detect browser profile for isolated browsing.
Pass the proxy details directly into your web automation scripts. For example, if you are using Python with Selenium for web automation, configuring your proxy takes just a few lines of code: